the cia manual of trickery and deception
This document, a fascinating glimpse into Cold War strategy, details methods for manipulating perceptions and influencing adversaries through calculated deceit and psychological warfare․
Historical Context & Origins
Emerging during the height of the Cold War, the CIA Manual of Trickery and Deception wasn’t a singular document but a collection of evolving techniques․ Its roots lie in the OSS (Office of Strategic Services) practices of World War II, refined through experiences countering Soviet influence․
Initially compiled in the 1950s, it was formally published in 1983, intended for operatives working in hostile environments․ The manual reflects a period defined by ideological conflict and a perceived need for unconventional warfare tactics to safeguard national interests․
Purpose and Intended Audience
The manual’s primary purpose was to equip CIA field operatives with the knowledge to conduct effective deception operations behind enemy lines․ It aimed to provide practical guidance on manipulating individuals, groups, and even entire populations to support US foreign policy objectives․
The intended audience consisted of case officers, intelligence gatherers, and those involved in psychological warfare․ It wasn’t designed for the general public, but rather as a confidential resource for professionals engaged in covert activities․
Core Principles of Deception
Successful deception relies on understanding human psychology, exploiting vulnerabilities, and crafting believable illusions to influence targets’ beliefs and actions effectively․
The Importance of Credibility
Establishing and maintaining credibility is paramount to any successful deception operation․ The manual stresses that a deceiver must initially be perceived as trustworthy and reliable․
This involves meticulous attention to detail, consistency in narratives, and avoiding obvious falsehoods early on․
A compromised credibility renders subsequent deceptions far more difficult, if not impossible, as the target will instinctively distrust any information presented․
Therefore, building a foundation of trust is the first, and often most crucial, step․
Exploiting Cognitive Biases
The manual highlights the significance of understanding and leveraging inherent human cognitive biases․ These predictable patterns in thinking – confirmation bias, anchoring effect, and availability heuristic – create vulnerabilities․
Deception can be amplified by presenting information that confirms pre-existing beliefs, framing narratives to influence perception, and exploiting the ease with which readily available information is accepted as truth․
By understanding these biases, operators can craft more effective and persuasive disinformation․
Maintaining Operational Security
Crucially, the manual emphasizes rigorous operational security (OPSEC) as paramount to successful deception․ Compromised security unravels even the most ingenious schemes, exposing agents and undermining operations․
This includes meticulous communication protocols, secure document handling, and awareness of surveillance risks․
Minimizing digital footprints, utilizing secure locations, and employing counter-surveillance techniques are vital․
Maintaining anonymity and preventing attribution are core tenets of effective covert action․
Techniques for Disinformation
Disinformation relies on crafting and disseminating false or misleading information to influence opinions, behaviors, and ultimately, strategic outcomes for desired effects․
Creating False Narratives
The manual emphasizes constructing believable, yet entirely fabricated, stories to shape perceptions․ This involves identifying existing beliefs and vulnerabilities within a target audience․
Successful narratives often incorporate elements of truth, subtly interwoven with falsehoods, making them harder to detect․
Key to this technique is consistent repetition and leveraging multiple channels – media, rumors, and seemingly independent sources – to reinforce the fabricated account and establish its perceived legitimacy․
Utilizing Propaganda Effectively
The manual details propaganda’s power, not through overt lies, but by selectively presenting facts and framing information to elicit a desired emotional response․
Understanding the target audience’s values, fears, and prejudices is crucial for crafting persuasive messages․
Repetition, simplification, and appealing to popular sentiments are highlighted as key techniques․
Effective propaganda, according to the manual, avoids complex arguments, favoring emotionally charged symbols and slogans for maximum impact and widespread acceptance․
The Role of “Black” Propaganda
“Black” propaganda, attributed to a false source, is presented as a particularly potent, though ethically questionable, tool․
The manual emphasizes its effectiveness in discrediting opponents and sowing discord by creating the illusion of internal conflict within enemy ranks․
Successfully implemented, it can damage morale and undermine trust in leadership․
However, the document acknowledges the risks of exposure, which could backfire and damage the credibility of the originating intelligence agency․
Methods of Covert Communication
Secure exchanges relied on ingenious techniques – dead drops, coded messages, and intermediaries – ensuring clandestine information transfer while minimizing detection risks․
Dead Drops and Signals
Dead drops, pre-arranged, concealed locations, facilitated anonymous exchanges of materials or messages․ These ranged from innocuous public sites – a loose brick in a wall, a hollowed-out book – to more elaborate, hidden containers․
Signals, often subtle and pre-determined, indicated when a drop was ready or if a meeting was compromised․ These could involve chalk marks, specific items placed in windows, or even seemingly random events with coded meanings․
Success hinged on meticulous planning, operational security, and a deep understanding of the environment to avoid counter-surveillance and maintain secrecy․
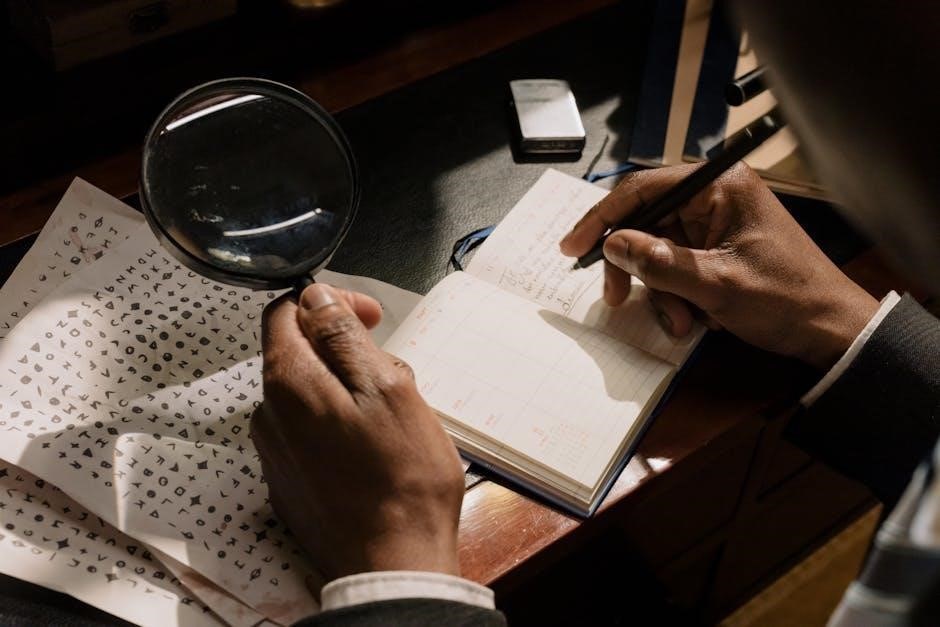
Ciphers and Codes
Secure communication relied heavily on ciphers and codes, transforming plaintext into unintelligible forms․ The manual detailed various methods, from simple substitution ciphers – replacing letters with others – to more complex polyalphabetic ciphers, like the Vigenère cipher, offering increased security․
One-time pads, considered unbreakable when used correctly, were also covered․
Agents needed proficiency in encoding and decoding, alongside strict protocols for key distribution and management to prevent compromise․ Maintaining secrecy of these methods was paramount to operational success․
Using Cutouts and Front Organizations
To obscure CIA involvement, the manual advocated utilizing “cutouts” – intermediaries who acted on the agency’s behalf without direct knowledge of its source․ These individuals provided a layer of deniability․
Furthermore, establishing “front organizations” – seemingly independent groups funded and guided by the CIA – allowed for covert influence operations․
These fronts could disseminate propaganda, fund political activities, or gather intelligence, all while masking the agency’s hand․
Psychological Manipulation Tactics
The manual extensively covers exploiting human vulnerabilities, employing techniques to subtly alter perceptions, behaviors, and beliefs for intelligence gathering and operational success․
Exploiting Emotional Vulnerabilities
The manual details how to identify and leverage an individual’s emotional weaknesses – fear, greed, vanity, or patriotism – to gain influence․
Techniques involve appealing to these feelings, creating situations that trigger desired responses, and subtly manipulating perceptions to exploit pre-existing biases․
Understanding cultural nuances and individual psychology is crucial for effectively employing these tactics, maximizing control and eliciting cooperation without raising suspicion․
This approach prioritizes psychological pressure over physical coercion․
Building Rapport and Trust
Before any manipulation can succeed, establishing a connection with the target is paramount․
The manual emphasizes mirroring behavior, active listening, and feigning shared values to create a sense of camaraderie․
Agents are instructed to identify the target’s interests and demonstrate genuine (or convincingly simulated) enthusiasm, fostering a feeling of mutual understanding․
This carefully constructed trust serves as the foundation for subsequent deception․
The Use of Suggestion and Hypnosis
The manual explores subtle techniques of suggestion, aiming to implant ideas without overt coercion․
While not advocating full-blown hypnosis, it details methods to induce a state of heightened suggestibility through carefully crafted language and repetitive phrasing․
Creating ambiguity and exploiting gaps in the target’s reasoning are key․
Agents learn to frame information in a way that subtly guides the target towards desired conclusions, bypassing critical thought․
Counter-Deception Strategies
Recognizing manipulative tactics requires critical thinking, source verification, and awareness of cognitive biases to dismantle disinformation and protect against influence․
Identifying Disinformation Campaigns
Detecting orchestrated disinformation requires a multi-faceted approach․ Look for patterns of coordinated messaging across multiple platforms, often amplified by bot networks or fake accounts․
Analyze the source’s credibility – is it a known entity with a history of accuracy, or a newly created, anonymous account?
Be wary of emotionally charged content designed to provoke a reaction rather than inform․
Cross-reference information with multiple, independent sources to verify its accuracy and identify inconsistencies․
Verifying Information Sources
Rigorous source verification is paramount when assessing information, especially in an environment rife with deception․
Investigate the source’s ownership, funding, and potential biases․
Check for a clear editorial policy and fact-checking procedures․
Consult reputable media watchdogs and fact-checking organizations like Snopes or PolitiFact․
Lateral reading – leaving the initial source to investigate the source itself – is crucial․
Consider the author’s expertise and reputation on the subject matter․
Protecting Against Psychological Manipulation
Cultivate critical thinking skills to analyze information objectively, resisting emotional appeals and cognitive biases․
Be aware of common manipulation tactics like gaslighting, fear-mongering, and appeals to authority․
Maintain healthy skepticism and question narratives that seem too good – or too bad – to be true․
Practice mindfulness and emotional regulation to avoid impulsive reactions․
Seek diverse perspectives and avoid echo chambers that reinforce existing beliefs․
Trust your instincts and prioritize your mental well-being․
Specific Deception Techniques Detailed in the Manual
The manual outlines crafting believable false identities, staging misleading events, and skillfully exploiting both media outlets and widespread public opinion effectively․
Creating False Identities
The manual dedicates significant attention to constructing entirely new personas, emphasizing meticulous background stories, consistent documentation, and believable behavioral patterns․ Agents were instructed to develop detailed life histories, including fabricated employment records, family connections, and even hobbies․
This involved mastering relevant skills and knowledge to convincingly portray the assumed identity under scrutiny․ The goal wasn’t simply impersonation, but the creation of a fully realized, independent existence capable of withstanding intense investigation and prolonged interaction․
Staging Events to Mislead
A core tactic involved orchestrating seemingly spontaneous incidents designed to shape perceptions and influence enemy actions․ This ranged from carefully planted rumors and fabricated evidence to deliberately engineered “accidents” or public displays․
The manual stresses the importance of plausibility and minimizing direct agency involvement․ Success hinged on creating events that appeared organic, aligning with existing beliefs, and subtly guiding adversaries towards predetermined conclusions, all while maintaining deniability․
Exploiting Media and Public Opinion
The manual recognizes the media as a powerful tool for shaping narratives and influencing public sentiment․ Techniques included cultivating relationships with journalists, feeding them carefully crafted stories, and utilizing propaganda to sway opinion․
Disinformation was strategically disseminated through various media channels – newspapers, radio, and later, television – to create a desired public perception, discredit opponents, and justify covert operations․ Maintaining plausible deniability was paramount in these efforts․

Ethical Considerations and Controversies
The manual’s techniques raise profound ethical questions regarding manipulation, truthfulness, and the justification of deception in the pursuit of national security objectives․
The Morality of Deception in Intelligence
The core dilemma lies in whether the ends – perceived national security benefits – justify the means of systematic deception․ Critics argue that intentionally misleading individuals, even adversaries, erodes trust and undermines democratic values․
Proponents contend that deception is a necessary evil, a tool for leveling the playing field against those who operate without ethical constraints․ This perspective often frames deception as self-defense, a means of protecting citizens and interests․
However, the potential for abuse and the long-term consequences of normalizing dishonesty remain significant concerns, fueling ongoing debate․
Legal Ramifications of Covert Operations
Covert actions, by their nature, often operate in a gray area of legality, frequently skirting the boundaries of domestic and international law․ While ostensibly authorized by higher authority, actions detailed in manuals like this can violate statutes prohibiting domestic spying or false statements․
International law presents further complications, particularly regarding sovereignty and intervention in other nations’ affairs․
Accountability is a major issue; plausible deniability shields operatives, making prosecution difficult, and raising questions about oversight and legal responsibility․
Public Perception and Transparency
The revelation of manuals detailing deceptive practices significantly erodes public trust in intelligence agencies․ Transparency, or the lack thereof, becomes central to the debate surrounding covert operations and their justification․
Maintaining secrecy clashes with democratic principles of accountability, fueling conspiracy theories and skepticism․
Balancing national security with the public’s right to know remains a persistent challenge, particularly when deception is acknowledged as a core tactic․
The Manual’s Impact on Modern Intelligence
The manual codified techniques still influencing intelligence gathering, shaping psychological operations, and informing strategies for countering disinformation in contemporary global conflicts․
Influence on Contemporary Practices
The manual’s principles permeate modern intelligence agencies, informing approaches to strategic communication, influence operations, and counterintelligence․ Its emphasis on understanding human psychology remains central to effective deception․
Contemporary practices demonstrate a clear lineage, from utilizing social media for disinformation campaigns to crafting narratives that shape public opinion․ The core tenets of credibility, exploiting biases, and maintaining security are consistently applied, albeit with updated tools and technologies․
Furthermore, the manual’s focus on creating and leveraging false identities continues to be relevant in the digital age, influencing methods of online persona creation and covert operations․
Lessons Learned and Adaptations
Analysis of the manual’s successes and failures highlighted the importance of adaptability and anticipating adversary responses․ Early reliance on simplistic narratives proved vulnerable to scrutiny, prompting a shift towards more nuanced and layered disinformation․
The rise of independent media and the internet necessitated adapting techniques to a fragmented information landscape․ Agencies learned to leverage multiple channels and cultivate “sleeper” networks for long-term influence;
Crucially, the manual underscored the need for continuous evaluation and refinement of deception strategies in the face of evolving technologies and public awareness․
Criticisms and Limitations
The manual faced criticism for its potential to erode public trust and undermine democratic processes․ Concerns arose regarding the ethical implications of widespread deception, even when framed as national security imperatives․
Its effectiveness diminished as media literacy increased and independent fact-checking became prevalent․
Furthermore, the manual’s focus on psychological manipulation proved less effective against sophisticated adversaries capable of recognizing and countering such tactics․
Over-reliance on deception also risked damaging an agency’s credibility if exposed․
Analyzing Case Studies
Examining historical events reveals how the manual’s principles were applied – and sometimes misapplied – with varying degrees of success and significant consequences․
Operation Mockingbird – A Historical Example
Allegedly beginning in the 1950s, Operation Mockingbird involved the CIA’s covert influence on US media․ The aim was to disseminate propaganda and shape public opinion during the Cold War․
Investigations revealed journalists were secretly employed by the CIA, producing biased news stories․ This raises serious ethical questions about journalistic integrity and the potential for government manipulation of information․
The program’s extent and impact remain debated, but it serves as a stark example of deception tactics detailed within the manual being put into practice․
The Iran-Contra Affair – Deception in Action
The Iran-Contra Affair, unfolding in the 1980s, showcased a complex web of deceit․ The US secretly sold arms to Iran, violating an arms embargo, and used the proceeds to fund the Contras in Nicaragua, defying a Congressional ban․
This involved deliberate misinformation to Congress and the public, concealing the true nature of these operations․
The affair exemplifies techniques from the manual – creating false narratives, utilizing cutouts, and maintaining operational security through layers of denial and obfuscation․
Modern Examples of Disinformation Campaigns
Contemporary disinformation campaigns, amplified by social media, echo techniques detailed in the manual․ The 2016 US Presidential election saw Russian interference through fabricated news stories and social media manipulation, aiming to sow discord and influence voters․
More recently, campaigns surrounding the COVID-19 pandemic spread false narratives about the virus’s origins and treatments;
These examples demonstrate the manual’s enduring relevance in a digital landscape, utilizing propaganda and exploiting cognitive biases at scale․
The Manual’s Relevance Today
Despite its age, the manual’s principles remain strikingly pertinent, particularly in navigating the complexities of modern information warfare and digital manipulation․
Deception in the Digital Age
The proliferation of social media and online platforms has dramatically expanded the scope and speed of potential deception operations․ Techniques outlined in the manual, such as creating false narratives and exploiting cognitive biases, are now readily amplified through algorithms and bot networks․
Disinformation campaigns can rapidly spread globally, influencing public opinion and potentially destabilizing political processes․ The anonymity afforded by the internet presents new challenges for attribution and counter-deception, demanding sophisticated analytical skills and technological solutions to combat these evolving threats․
Combating Online Misinformation
Drawing lessons from the CIA manual, effective countermeasures require a multi-faceted approach․ Critical thinking skills and media literacy are paramount, empowering individuals to question sources and identify manipulative tactics․
Fact-checking organizations play a vital role in debunking false claims, while platform accountability is crucial for curbing the spread of disinformation․ Developing robust detection algorithms and promoting transparency in online content moderation are essential steps in safeguarding information integrity․
Protecting Against Foreign Interference
The manual’s principles highlight the need for vigilance against subtle influence operations․ Strengthening national cybersecurity infrastructure is vital, alongside proactive monitoring of information ecosystems for malicious activity․
Counterintelligence efforts must focus on identifying and neutralizing foreign agents spreading disinformation․ Public-private partnerships are essential for sharing threat intelligence and coordinating defensive strategies․ Promoting democratic resilience through informed citizenry remains the strongest safeguard․

Resources for Further Research
Explore academic papers on psychological warfare, government investigations into covert actions, and insightful books detailing the world of intelligence operations․
Academic Studies on Deception
Numerous scholarly works dissect the psychology of deception, exploring its cognitive and emotional underpinnings․ Research delves into the effectiveness of various manipulative techniques, analyzing how biases and vulnerabilities are exploited․
Studies examine the ethical implications of deceptive practices, particularly within governmental and intelligence contexts․ Investigations into propaganda, misinformation, and strategic communication provide critical insights․
Furthermore, academic analyses assess the impact of deception on public opinion, political processes, and international relations, offering a nuanced understanding of its complexities․
Government Reports and Investigations
Official investigations, like the Church Committee Report, revealed past covert operations and questionable intelligence practices, including those aligning with the manual’s principles․
Government accountability reports often scrutinize the use of deception by intelligence agencies, focusing on oversight and legal compliance․
Declassified documents and Freedom of Information Act requests provide glimpses into internal agency policies regarding disinformation and psychological warfare, shedding light on operational realities․
Books and Documentaries on Intelligence
Numerous publications explore the world of espionage, with titles like “Legacy of Ashes” offering critical analyses of CIA operations and the impact of deceptive practices․
Documentaries, such as those focusing on the Church Committee, visually present historical investigations into intelligence abuses and the ethical dilemmas of covert action․
Biographies of intelligence officers and scholarly works on psychological warfare provide further context for understanding the techniques detailed within the manual․
The CIA manual, though a product of its time, reveals timeless principles of influence and manipulation that continue to resonate in modern contexts․
Its insights into human psychology and the power of narrative remain relevant, shaping strategies in fields beyond intelligence, including marketing and politics․
Understanding these techniques is crucial, not only for recognizing deception but also for safeguarding against its potentially harmful consequences in an increasingly complex world․